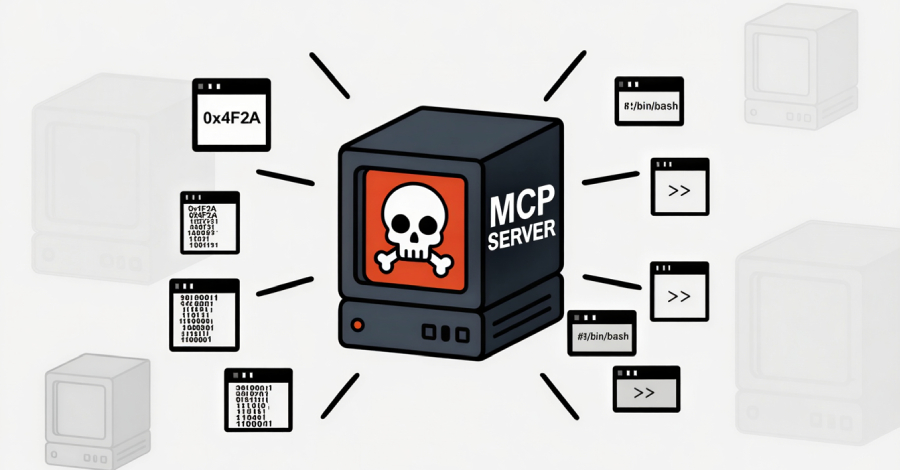
SmartLoader Attack Uses Trojanized Oura MCP Server to Deploy StealC Infostealer
Cybersecurity researchers have disclosed details of a new SmartLoader campaign that involves distributing a trojanized version of a Model Context Protocol (MCP) server associated with Oura Health to deliver an information stealer known as StealC. “The threat actors cloned a legitimate Oura MCP Server – a tool that connects AI assistants to Oura Ring health…
Read more