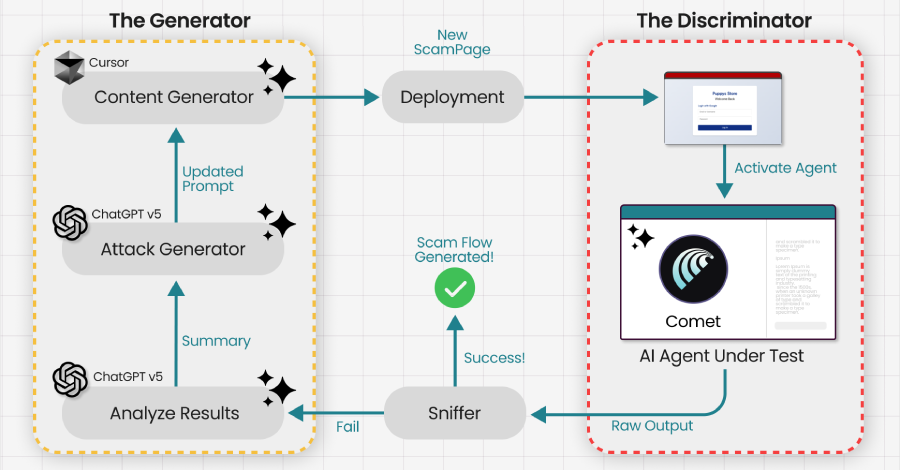
Researchers Trick Perplexity’s Comet AI Browser Into Phishing Scam in Under Four Minutes
Agentic web browsers that leverage artificial intelligence (AI) capabilities to autonomously execute actions across multiple websites on behalf of a user could be trained and tricked into falling prey to phishing and scam traps. The attack, at its core, takes advantage of AI browsers’ tendency to reason their actions and use it against the model…
Read more