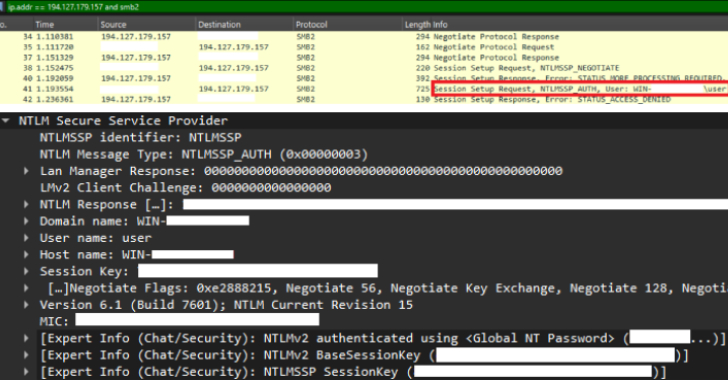
CVE-2025-24054 Under Active Attack—Steals NTLM Credentials on File Download
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a medium-severity security flaw impacting Microsoft Windows to its Known Exploited Vulnerabilities (KEV) catalog, following reports of active exploitation in the wild. The vulnerability, assigned the CVE identifier CVE-2025-24054 (CVSS score: 6.5), is a Windows New Technology LAN Manager (NTLM) hash disclosure